Digital technology continues to evolve, providing people with more ease and efficiency with various tasks. Many in-person activities, including opening bank accounts, shopping, and even healthcare consultations, already have electronic counterparts. With their mobile device, users can connect to the internet and access these online services.
According to Statista, the number of active internet users has reached 4.66 billion globally as of October 2020. About 91% of this population prefers to use mobile internet, making mobile technology the most-used channel for online access.
As different industries transition into a more digitally-dependent world, they are prompted to meet the rapidly changing demands for a better user experience and enhanced security on their platforms. It can be challenging for firms to verify if the person they are interacting with is who they say they are through remote services.
Fraudsters can use synthetic identities or impersonate someone else to exploit companies. To counter these criminal attacks, enterprises must adopt a scalable solution that will allow them to authenticate a large number of people trying to use their services at an efficient rate.
One way to shore up their identity authentication capabilities is by leveraging mobile biometric identification solutions. This identity proofing technology can be easily integrated into mobile devices, eliminating the need for extra hardware.
Users can simply take a selfie with their mobile device and undergo an anti-spoofing liveness detection test to complete the authentication process. When asked to provide an identity document, they can also use the same device to send a photo of their valid government ID for verification.
With mobile biometric identification, enterprises can harness the benefits of multi factor authentication (MFA) in deterring fraud. It provides a multi-layered defense to block criminals from infiltrating a user’s account. By enabling MFA, users will be asked to provide more than one authentication credential such as a password before being granted access to the system.
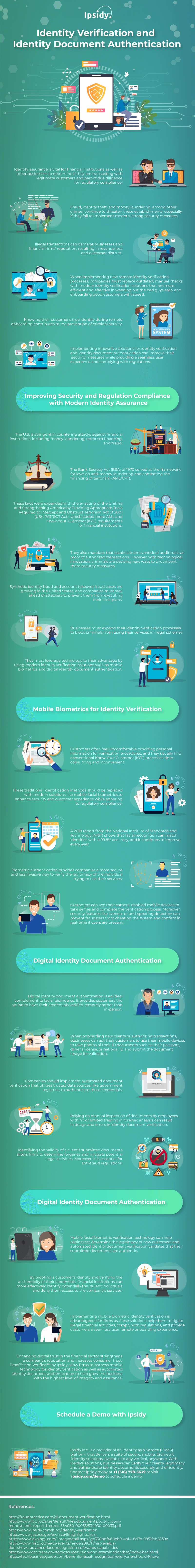
The need for robust security measures to filter out fraudulent individuals cannot be stressed enough. To know more about the matter, Ipsidy provides the following infographic.